Ensuring Data Security in a Post-Quantum Era: Quantum-Resistant Encryption Explained
The advent of quantum computing has sparked concerns about the security of our digital world. As quantum computers become more powerful, they will be able to break certain types of encryption that are currently used to protect data. This raises the question: how can we ensure the security of our data in a post-quantum era? The answer lies in quantum-resistant encryption algorithms.
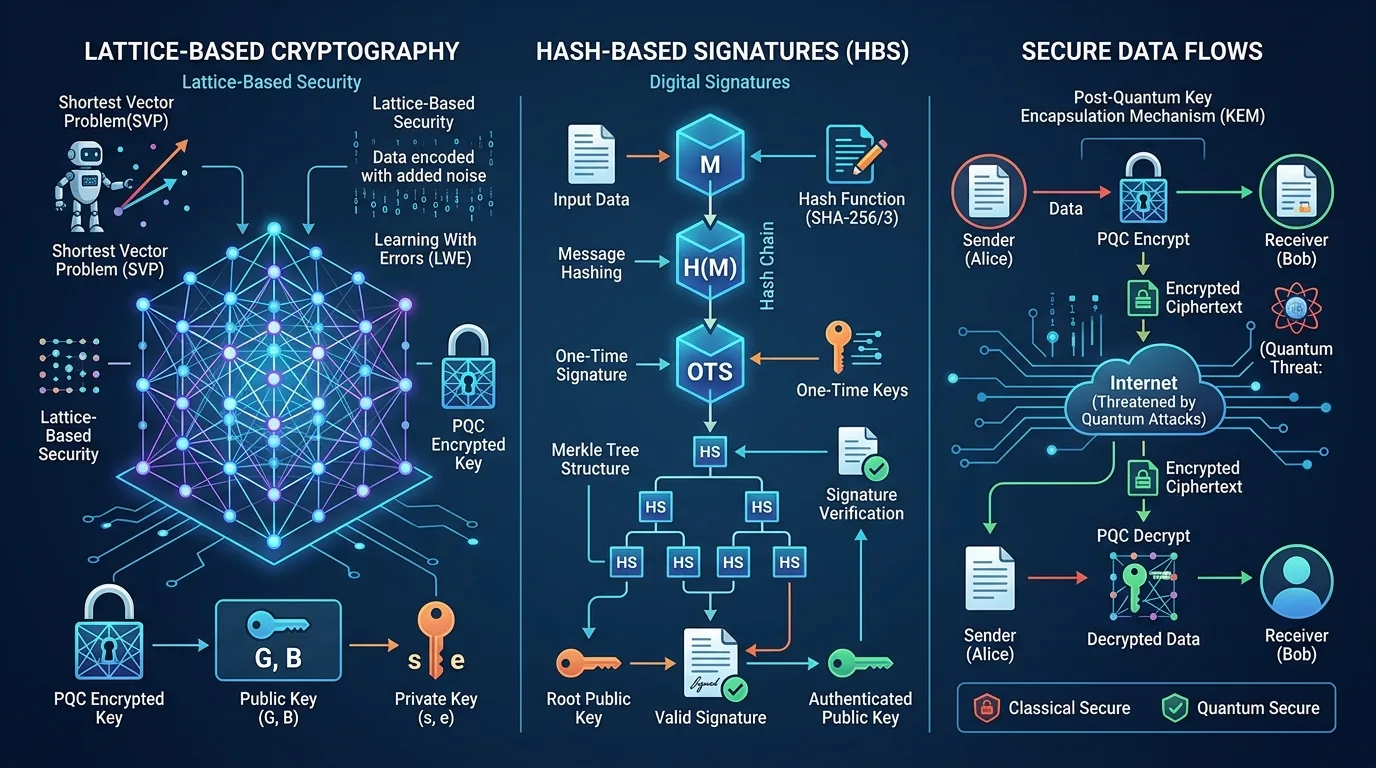
Quantum-resistant encryption is designed to withstand attacks from both classical and quantum computers. These algorithms use advanced mathematical techniques, such as lattice-based cryptography and hash-based signatures, to provide unparalleled security. In this article, we will delve into the world of quantum-resistant encryption and explore its benefits for future-proofing data security.

What are Quantum-Resistant Encryption Algorithms?
Quantum-resistant encryption algorithms are designed to be resistant to attacks from both classical and quantum computers. These algorithms use advanced mathematical techniques, such as lattice-based cryptography and hash-based signatures, to provide unparalleled security.
Some examples of quantum-resistant encryption algorithms include:
Lattice-Based Cryptography: This type of cryptography uses the hardness of the shortest vector problem in a lattice to secure data. Lattice-based cryptography is considered to be one of the most promising approaches to post-quantum cryptography.
+ Think of a lattice as a three-dimensional array of points, where each point has a specific set of coordinates. The shortest vector problem involves finding the closest point to the origin (0, 0, 0) in this lattice. This problem is computationally difficult for both classical and quantum computers, making it an ideal candidate for post-quantum cryptography.
Hash-Based Signatures: These signatures use hash functions to create digital signatures that are resistant to quantum attacks.
+ A hash function takes input data of any size and produces a fixed-size output, known as the hash value. Hash-based signatures use these hash values to verify the authenticity of data. Quantum-resistant hash-based signatures ensure that even if an attacker tries to manipulate the data, the signature will remain intact.
Code-Based Cryptography: This type of cryptography uses error-correcting codes to secure data. Code-based cryptography is another promising approach to post-quantum cryptography.
Benefits of Quantum-Resistant Encryption
Quantum-resistant encryption algorithms offer several benefits for future-proofing data security. Some of the key advantages include:
Resistance to Quantum Attacks: Quantum-resistant encryption algorithms are designed to withstand attacks from both classical and quantum computers.
+ This is because these algorithms use advanced mathematical techniques that are resistant to both classical and quantum attacks.
Improved Security: These algorithms use advanced mathematical techniques to provide unparalleled security.
+ For example, lattice-based cryptography provides a high level of security by relying on the hardness of the shortest vector problem in a lattice.
Future-Proofing: Quantum-resistant encryption algorithms will continue to provide secure data protection even as quantum computers become more powerful.
Implementing Quantum-Resistant Encryption
Implementing quantum-resistant encryption is a complex task that requires careful consideration of several factors. Some key considerations include:
Key Management: Quantum-resistant encryption requires the use of large, random keys that are difficult to factorize.
+ Key management involves generating and storing these large, random keys securely.
Algorithm Selection: The choice of algorithm will depend on specific requirements and constraints.
+ For example, if a system requires high-speed encryption, lattice-based cryptography might be a suitable choice. On the other hand, if security is the top priority, hash-based signatures might be preferred.
Performance: Quantum-resistant encryption algorithms can be computationally intensive.
Practical Applications of Quantum-Resistant Encryption
Quantum-resistant encryption has several practical applications in various industries. Some examples include:
Secure Communication Networks: Quantum-resistant encryption is essential for secure communication networks, such as those used by governments and financial institutions.
+ These networks rely heavily on secure data transmission to prevent eavesdropping and tampering.
Data Storage: Quantum-resistant encryption can be used to protect data stored on devices, such as laptops and smartphones.
+ This ensures that even if a device is lost or stolen, the data remains secure.
Cloud Computing: Cloud providers use quantum-resistant encryption to protect customer data.
Addressing Common Concerns
Some common concerns about quantum-resistant encryption include:
Performance Overhead: Some argue that quantum-resistant encryption requires significant computational resources, which can lead to performance overhead.
+ However, this concern is often based on a misunderstanding of the technology. Quantum-resistant encryption algorithms are designed to provide secure data protection, not to compromise performance.
Key Management Complexity: The management of large, random keys required by quantum-resistant encryption algorithms can be complex and time-consuming.
+ This complexity can be mitigated with proper key management practices.
Case Studies
Several organizations have successfully implemented quantum-resistant encryption in their systems. Some examples include:
Google's BoringSSL: Google has developed an open-source SSL/TLS library called BoringSSL that uses quantum-resistant encryption algorithms.
+ BoringSSL provides a secure and efficient way to encrypt data transmitted over the internet.
Cloud providers' use of quantum-resistant encryption: Cloud providers like Amazon Web Services (AWS) and Microsoft Azure have implemented quantum-resistant encryption in their cloud storage solutions.
Conclusion
Quantum-resistant encryption is a crucial step towards securing our digital world against the threats posed by quantum computers. By understanding the benefits and implementation requirements of these algorithms, we can ensure that our data remains secure even as quantum computers become more powerful.




