Quantum-Resistant Encryption: Protecting Data in a Post-Quantum World
The advent of quantum computing has sent shockwaves through the tech industry, and for good reason. As these powerful machines begin to emerge, they pose an existential threat to traditional encryption methods. For decades, we've relied on algorithms like RSA and elliptic curve cryptography to safeguard our data. However, these methods are vulnerable to attacks by quantum computers, which could potentially break even the most secure encryption codes in a matter of minutes.
In this article, we'll delve into the world of quantum-resistant encryption, exploring what it is, how it differs from traditional methods, and why it's essential for protecting our data in a post-quantum world. We'll examine the latest trends in quantum-resistant encryption algorithms, their benefits, and real-world applications.
What is Quantum-Resistant Encryption?
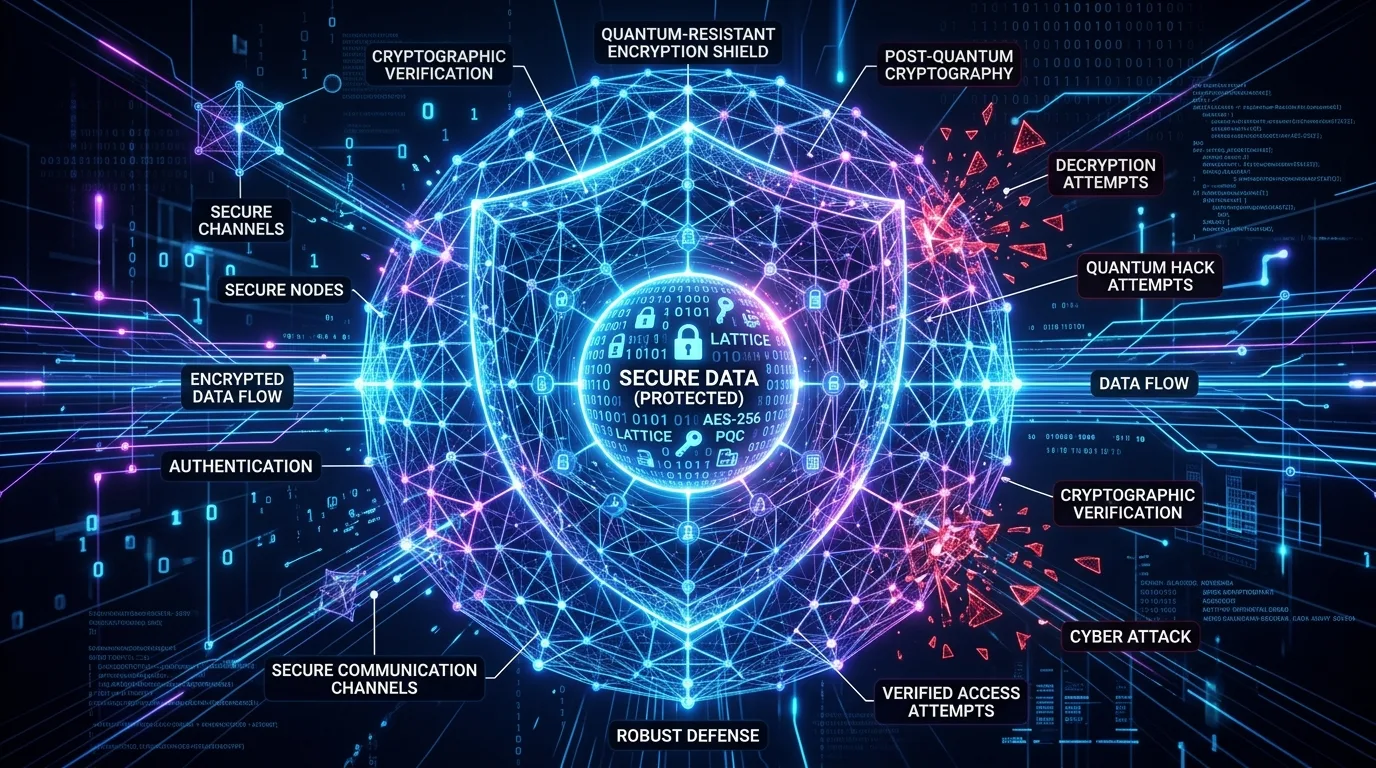
Quantum-resistant encryption refers to cryptographic techniques designed to withstand attacks by powerful quantum computers. These algorithms use advanced mathematical concepts, such as lattice-based cryptography and hash-based signatures, to ensure the security of our data. Unlike traditional encryption methods, which rely on the difficulty of factoring large numbers or computing discrete logarithms, quantum-resistant encryption relies on the hardness of problems that are intractable for both classical and quantum computers.
Think of it like this: traditional encryption methods use a combination lock with a finite number of combinations. A quantum computer can try an enormous number of combinations in a very short time, making it possible to break the encryption code. Quantum-resistant encryption uses a more complex combination lock that is virtually impossible for both classical and quantum computers to crack.
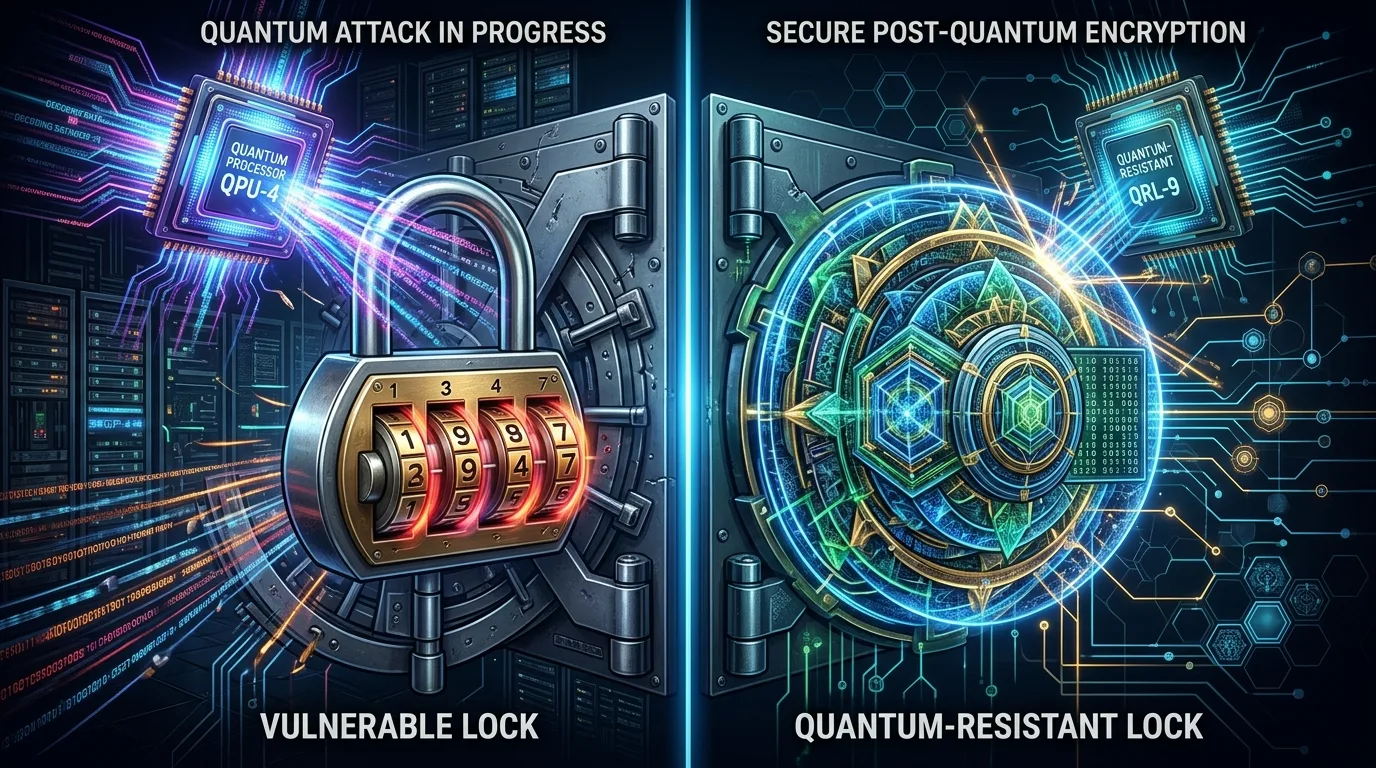
To better understand this concept, let's consider an example. Imagine a secure online banking system that relies on traditional RSA encryption. A hacker with access to a powerful quantum computer could potentially break into the system by factoring large numbers or computing discrete logarithms. However, if the bank were to switch to a quantum-resistant encryption algorithm, such as lattice-based cryptography or hash-based signatures, it would be much more difficult for even the most advanced hackers to gain unauthorized access.
Key Features of Quantum-Resistant Encryption
Some key features of quantum-resistant encryption algorithms include:
• Post-quantum security: These algorithms are designed to remain secure even if a large-scale quantum computer becomes available.
• Classical resistance: They also provide robust protection against attacks by classical computers, ensuring data security in the short term.
• Efficiency: Quantum-resistant encryption algorithms often offer improved performance compared to traditional methods, making them suitable for widespread adoption.
• Flexibility: These algorithms can be integrated with existing cryptographic infrastructure, facilitating a smooth transition to post-quantum security.
It's essential to note that quantum-resistant encryption is not just about protecting against quantum computers. It also provides robust protection against attacks by classical computers, ensuring data security in the short term. This dual approach makes quantum-resistant encryption an attractive solution for organizations looking to safeguard their sensitive data.
Benefits of Quantum-Resistant Encryption
The benefits of quantum-resistant encryption are numerous:
• Future-proofing data security: By adopting these algorithms, organizations can ensure the long-term security of their sensitive data.
• Protection against advanced threats: Quantum-resistant encryption provides robust protection against sophisticated attacks from both classical and quantum computers.
• Improved performance: Many quantum-resistant encryption algorithms offer improved efficiency and speed compared to traditional methods.
To illustrate this point, consider a company that handles sensitive customer information. In the short term, they may be protected by traditional encryption methods. However, if a large-scale quantum computer becomes available in the future, these methods may no longer be sufficient. By adopting quantum-resistant encryption algorithms, the company can ensure the long-term security of their data and protect against advanced threats.
Another benefit of quantum-resistant encryption is its improved performance compared to traditional methods. Many quantum-resistant encryption algorithms offer faster processing speeds and reduced latency, making them suitable for widespread adoption. This is particularly important for applications that require high-speed encryption, such as online banking or cloud storage services.
Applications and Adoption
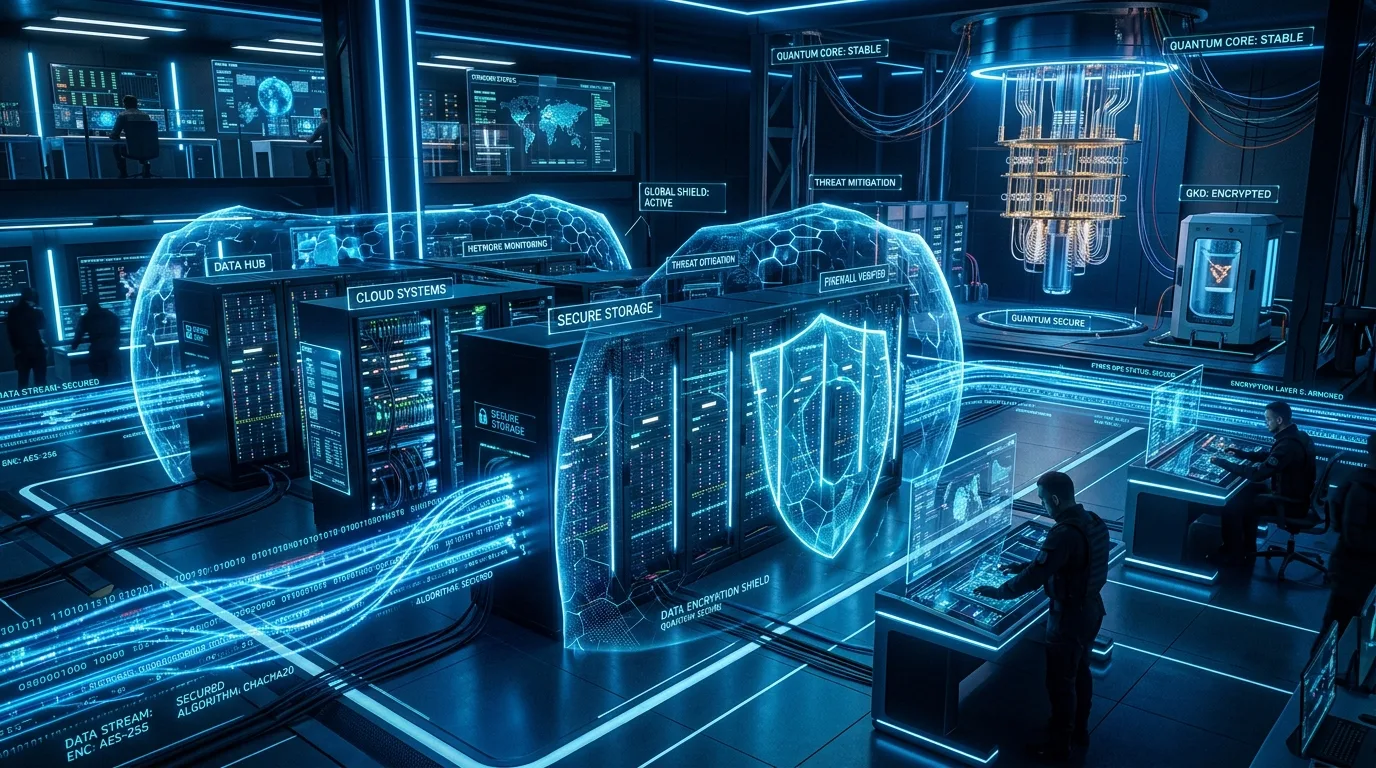
While quantum-resistant encryption is still a developing field, several organizations have already begun adopting these technologies:
In 2020, the US National Institute of Standards and Technology (NIST) announced the selection of four quantum-resistant encryption algorithms for further development: NTRU-HRSS, CRYSTALS-Kyber, CRYSTALS-Dilithium, and SPHINCS.
These developments demonstrate the growing interest in quantum-resistant encryption and its potential to revolutionize data security.
It's worth noting that the adoption of quantum-resistant encryption is not limited to government agencies or large corporations. Any organization that handles sensitive data can benefit from implementing quantum-resistant encryption algorithms. This includes financial institutions, healthcare providers, and online retailers, among others.
Implementation Considerations
Implementing quantum-resistant encryption algorithms requires careful consideration of several factors, including:
Key management: Quantum-resistant encryption algorithms often require more complex key management systems to ensure secure key exchange and storage.
Performance optimization: Organizations must carefully optimize the performance of their quantum-resistant encryption algorithms to minimize latency and maximize throughput.
Interoperability: Quantum-resistant encryption algorithms may not be compatible with existing cryptographic infrastructure, requiring organizations to invest in new hardware and software solutions.
Despite these challenges, many organizations are already exploring the benefits of quantum-resistant encryption. By adopting these technologies, they can ensure the long-term security of their sensitive data and protect against advanced threats from both classical and quantum computers.
Conclusion
Quantum-resistant encryption is a rapidly evolving field that holds significant promise for improving data security in a post-quantum world. With its improved performance, flexibility, and robust protection against advanced threats, quantum-resistant encryption is an attractive solution for organizations looking to safeguard their sensitive data. As the development of quantum-resistant encryption algorithms continues to advance, we can expect to see increased adoption across various industries and applications.
References
National Institute of Standards and Technology (NIST). (2020). Post-Quantum Cryptography.
European Telecommunications Standards Institute (ETSI). (2019). Quantum-Secure Direct Communication Protocol for Secure Communication Networks.




