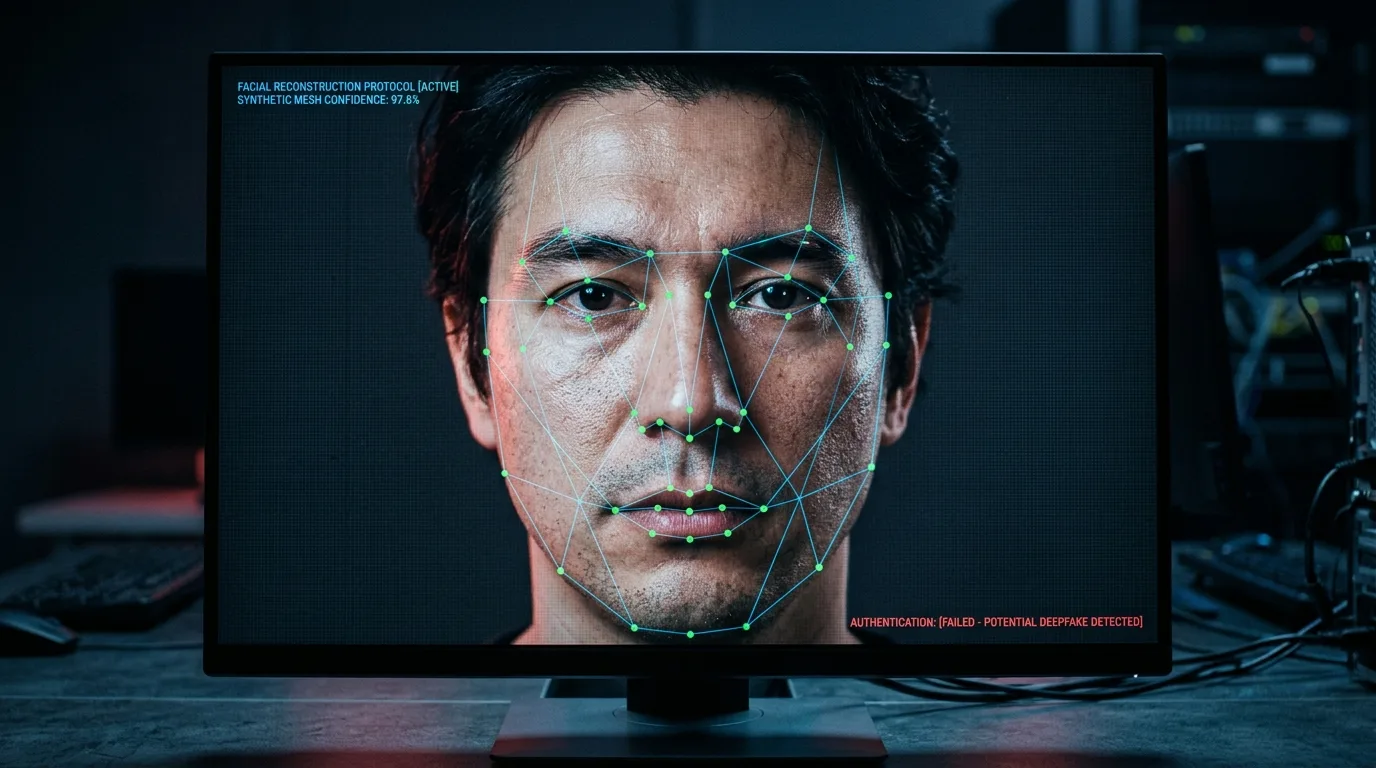
The internet has become an integral part of our daily lives, and with its increasing reliance on digital communication, cybersecurity threats have also evolved. One such threat is phishing via deepfake videos, which can deceive even the most cautious individuals. This article will delve into the world of deepfakes, explaining what they are, how they work, and most importantly, how to protect yourself from this growing cybersecurity menace.
How Do Deepfakes Work?
Deepfakes work by using machine learning algorithms to analyze a dataset of video or audio recordings and then generate new content that resembles the original. This process is often referred to as "transfer learning," where the AI model learns from one task (e.g., identifying faces) and applies it to another task (e.g., creating fake videos).
The creation of deepfakes involves several steps:
Data collection: Gathering a dataset of video or audio recordings, which can be obtained from various sources, including social media platforms.
Model training: Using machine learning algorithms to train the model on the collected data, allowing it to learn patterns and characteristics of the original content.
Generation: The trained model generates new content based on the learned patterns, creating a deepfake video or audio recording.
Phishing via Deepfakes: A Growing Threat

Deepfakes have become a significant concern for cybersecurity experts as they can be used to launch sophisticated phishing attacks. These attacks typically involve sending a malicious email or message containing a deepfake video that appears to come from a trusted sender. The goal is to trick the recipient into revealing sensitive information, such as login credentials or financial data.
For instance, an attacker might create a deepfake video of a CEO asking employees to reset their passwords due to a "security update." Unbeknownst to the employees, the email is a phishing attempt designed to compromise the company's security.
Identifying Phishing Attacks via Deepfakes
Recognizing a phishing attack via deepfake video can be challenging, but there are some red flags to look out for:
Unusual sender: Be wary of emails or messages from unknown senders, especially if they claim to be from someone you trust.
Urgency: If the message creates a sense of urgency, such as "your account will be suspended if you don't take action now," it's likely a phishing attack.
Suspicious links: Hover over any links in the email or message to see the actual URL. If it appears suspicious or is from an unfamiliar domain, do not click on it.
It's essential to remember that legitimate companies typically have professional communication standards, and emails or messages with typos or grammatical errors may be a sign of a phishing attempt.
Verifying Sender Authenticity
To ensure sender authenticity, follow these steps:
Check the sender's email address: Verify that the email address matches the one you know.
Look for typos and grammatical errors: Legitimate companies typically have professional communication standards.
Be cautious of generic greetings: If an email or message uses a generic greeting (e.g., "Dear customer"), it may be a phishing attempt.
Protecting Yourself from Phishing via Deepfakes
To protect yourself from phishing attacks via deepfakes, follow these best practices:
Use strong passwords and enable two-factor authentication. This will make it more difficult for attackers to gain access to your account.
Keep your software and operating system up to date with the latest security patches. This will ensure that you have the latest security features and bug fixes.
Be cautious when clicking on links or opening attachments from unknown sources. This is especially true if the link or attachment appears suspicious or comes from an unfamiliar domain.
Verify sender authenticity by checking the email address, looking for typos or grammatical errors, and being cautious of generic greetings.
Conclusion
Phishing via deepfake videos is a growing cybersecurity threat that can deceive even the most cautious individuals. By understanding how deepfakes work, recognizing the red flags of phishing attacks, and taking steps to protect yourself, you can reduce the risk of falling victim to these types of attacks. Remember, it's always better to err on the side of caution when dealing with emails or messages that seem suspicious.
In conclusion, staying informed about cybersecurity threats is crucial in today's digital age. By being aware of the risks and taking steps to protect yourself, you can enjoy the benefits of online communication while minimizing the risks of phishing via deepfakes.
